Do you know most cybersecurity breaches originate at endpoints such as laptops, workstations, servers and mobile devices? Half a decade ago, the attack surface further expanded with remote work, BYOD and cloud-first environments. Today, a new dimension of risk has emerged: AI-powered attack tooling. Threat actors use generative AI to craft highly evasive malware, automate reconnaissance, and accelerate exploitation, often faster than traditional defences can respond.
So, how do you protect endpoints which are no longer confined to office walls? With best EDR tools for defending your organization in the digital age.
Endpoint Detection and Response (EDR) is a must-have for modern defence. Because it offers immense capabilities ranging from threat detection and deep visibility to swift remediation and forensic-level insights.
Based on our professional experience in the industry, peer reviews and customer talk points, we have curated this EDR tools list. Depending on your requirements, these EDR tools can strengthen your organizational security posture.
What is an EDR Tool?
Before jumping into the EDR tools list, find out what is EDR tool and how it helps security teams.
An Endpoint Detection and Response (EDR) tool is designed to detect, investigate and respond to suspicious activities or anomalous behaviour across endpoints in real time. It gathers rich telemetry, from processes, behaviours, file activity, and applies advanced analytics to uncover both known and novel threats.
Unlike traditional antivirus, which operates on signature-based detection, EDR solutions look for behaviours, lateral movement, privilege escalation and persistence mechanisms, offering security teams the context they need to act quickly and decisively.
Related Content: Endpoint Detection and Response (EDR): The Cornerstone of Modern Cyber Defence
How EDR Tools Work?
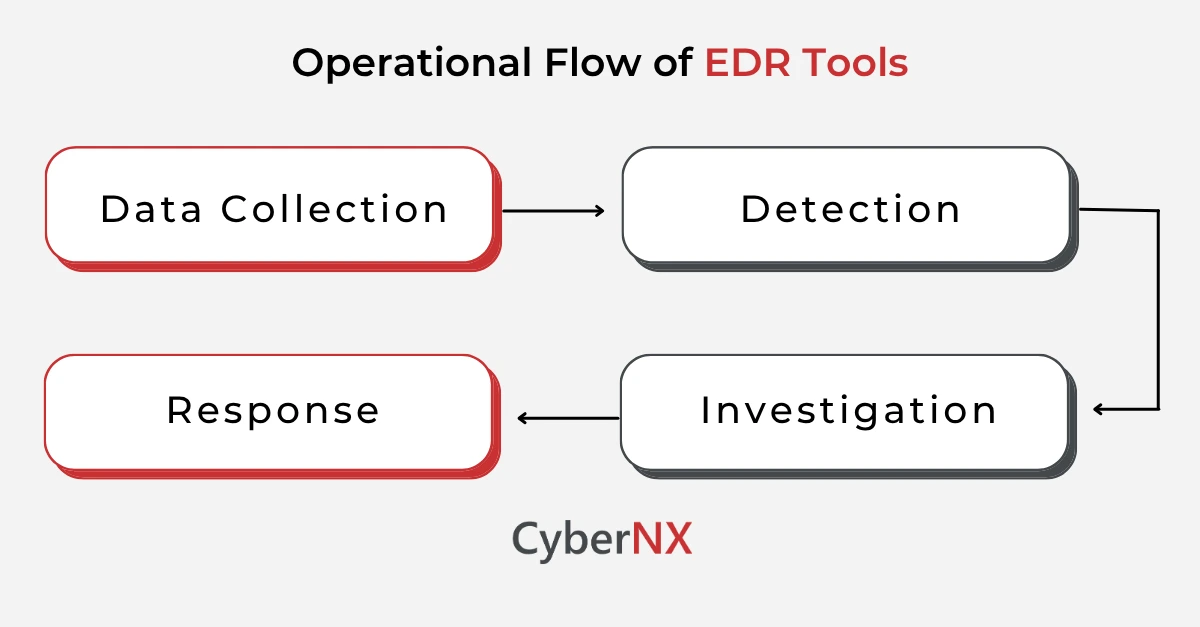
EDR platforms with specialized sensors are active participants in threat defence. Their operation generally follows four phases:
- Data Collection: Real-time data collection from endpoints—covering applications, memory, network activity, registry, and user behaviour.
- Detection: Use of behavioural analytics, AI, machine learning, and threat intelligence to spot anomalies and malicious activities.
- Investigation: Offering contextualized alerts, attack timelines and forensic details to trace threats to their source.
- Response: Containment of infected endpoints, terminating malicious processes and bringing back systems to pre-infection states automatically.
This powerful system minimizes the dwell time of threat actors inside your system and enables fast remediation.
Top 9 EDR Tools List in 2026
Here is our curated list for 2026, based on independent testing results, analyst research, and verified user feedback.
1. CrowdStrike Falcon
Best for: Large enterprises and mature SOCs requiring best-in-class detection
CrowdStrike Falcon is widely regarded as the market leader for cloud-native EDR. Its Threat Graph technology processes trillions of events weekly, and the platform consistently scores highest in independent testing – including MITRE ATT&CK evaluations, SE Labs, and AV-TEST – offering the best combination of detection accuracy, investigation tooling, and managed services.
Key features:
- Lightweight Agent: Single agent under 25 MB with sub-second response times and minimal endpoint performance impact.
- AI-Driven Threat Intelligence: Tracks over 200 named adversary groups globally, feeding real-time intelligence into detection logic.
- Threat Graph Correlation: Cloud-native graph engine correlates endpoint, identity, and cloud telemetry for cross-domain visibility.
- Falcon XDR: Extends EDR into full XDR, correlating threats across endpoints, cloud workloads, and identity systems.
- Incident Response Playbooks: Deep integration with threat intelligence and automated IR playbooks for post-detection agility.
2. SentinelOne Singularity
Best for: Enterprises requiring autonomous, machine-speed threat neutralisation
SentinelOne is known for its autonomous remediation and rollback capabilities. Its behavioural AI engine operates at machine speed, neutralising threats without needing cloud queries — making it effective even in air-gapped or low-connectivity environments. It also offers zero-trust posture management, container visibility, and rich forensic context.
Key features:
- Autonomous AI Engine: Detects and responds to threats without human intervention or cloud dependency, at machine speed.
- ActiveEDR + Storyline: Automatically maps all related events into a single attack storyline, dramatically reducing investigation time.
- Ransomware Rollback: 1-Click rollback to restore endpoints to a clean state after a ransomware attack.
- Zero-Trust Integration: Native identity and cloud workload visibility with zero-trust posture controls.
- Container & Cloud Security: Extends protection to Kubernetes, Docker, and cloud workloads seamlessly.
3. Microsoft Defender for Endpoint
Best for: Microsoft 365 environments and organisations seeking cost-effective, integrated protection
Microsoft Defender for Endpoint offers deep integration with the Microsoft security stack, leveraging the company’s vast global telemetry. For organisations already using Microsoft 365, it provides seamless protection with centralised management, and is increasingly competitive as a standalone EDR solution – not just a bundled afterthought.
Key features:
- Microsoft Ecosystem Integration: Native integration with Azure AD, Microsoft Sentinel, Intune, and the full Microsoft 365 security suite.
- Automated Investigation & Response (AIR): Fully automated investigation workflows that triage and remediate threats without analyst intervention.
- Threat & Vulnerability Management: Built-in risk-based vulnerability management tied to endpoint exposure scoring.
- Global Telemetry: Draws on signals from billions of endpoints, emails, and identities across the Microsoft customer base.
- Cost Efficiency: Bundled with M365 E5 licences, offering strong value for Microsoft-heavy environments.
4. Huntress Managed EDR
Best for: SMBs and MSPs seeking fully managed 24/7 protection without building an in-house SOC
Huntress Managed EDR is the standout choice in 2026 for organisations that want expert-backed endpoint coverage without the overhead of enterprise pricing or complex configuration. Rated #1 in MDR on PeerSpot with a 9.4 rating, it combines purpose-built detection with a 24/7 human SOC that triages, investigates, and responds on your behalf – filtering 95% of alerts before they reach your team.
Key features:
- 24/7 Human SOC: Expert analysts handle investigation and response around the clock, with a false positive rate below 1%.
- Persistent Foothold Detection: Uniquely effective at detecting attacker persistence mechanisms that slip past automated-only tools.
- Same-Day Deployment: Pre-built RMM scripts enable rapid rollout across large endpoint fleets – ideal for MSPs.
- Microsoft 365 + Identity Coverage: Extends protection to Microsoft 365 identities and Google Workspace, covering the full attack surface.
- Flat-Rate Transparent Pricing: Single-tier pricing with no hidden add-ons – designed for SMB and MSP budget predictability.
5. Cortex XDR (Palo Alto Networks)
Best for: Enterprises consolidating security operations across endpoint, network, and cloud
Cortex XDR from Palo Alto Networks merges data from endpoint, network, cloud, and identity sources into a single investigative timeline. In 2026, Palo Alto enhanced the platform with AgentiX Assistant AI agents that autonomously investigate alerts and execute response actions. ML-driven analytics significantly reduce alert fatigue and offer guided investigations.
Key features:
- Converged Data Lake: Unifies endpoint, network, cloud, and identity telemetry into one platform for cross-domain correlation.
- AgentiX AI Agents: Autonomous AI agents investigate alerts and execute response actions, reducing analyst triage burden.
- MITRE ATT&CK Coverage: Consistently high scores in MITRE ATT&CK evaluations for detection coverage and technique visibility.
- Palo Alto Ecosystem Integration: Native integration with NGFW, Prisma Cloud, and attack surface management tools.
- Guided Investigation: ML-driven alert grouping and investigation timelines reduce mean time to respond (MTTR) significantly.
6. Sophos Intercept X
Best for: Mid-market organisations seeking strong ransomware protection with easy management
Sophos Intercept X combines deep learning AI, exploit prevention, and EDR capabilities in a solution that is both powerful and easy to administer. Its CryptoGuard technology specifically targets ransomware with behavioural detection, rolling back encrypted files even mid-attack. Sophos also offers Managed Detection and Response (MDR) as a service layer for teams without a dedicated SOC.
Key features:
- CryptoGuard Ransomware Rollback: Detects and reverses unauthorised file encryption – even for novel, never-seen-before ransomware variants.
- Deep Learning Engine: Neural network-based malware detection that operates without signatures.
- Anti-Exploit Technology: Stops exploit techniques at the memory level, protecting against zero-days and fileless attacks.
- Sophos MDR: Fully managed threat hunting and response service – one of the most mature MDR offerings in this tier.
- Synchronised Security: Integrated security across firewall, email, and mobile for cohesive endpoint protection.
7. Cynet 360 AutoXDR
Best for: Small to mid-sized teams wanting broad security coverage in a single platform
Cynet 360 AutoXDR bundles EDR, NGAV, deception technology, network analytics, and user behaviour analytics (UBA) in a single platform. Its automation-first design allows response workflows to isolate machines, disable user accounts, and trigger alerts without human intervention — making it an excellent fit for lean security teams that need breadth without complexity.
Key features:
- Automation-First Response: Response workflows operate autonomously – isolating endpoints, disabling accounts, and alerting without manual steps.
- Deception Technology: Deploys decoys and honeytokens across the environment to detect lateral movement early.
- User Behaviour Analytics (UBA): Detects insider threats and compromised credentials through continuous behavioural baselining.
- Network Analytics: Extends detection beyond the endpoint to identify suspicious lateral movement and C2 communication.
- CyOps MDR: 24/7 managed detection and response service available within the platform at no additional cost.
8. FortiEDR (Fortinet)
Best for: Fortinet-heavy environments requiring unified security architecture
FortiEDR excels in pre-execution detection and real-time event correlation, stopping threats before they materialise into breaches. As part of Fortinet’s Security Fabric, it is particularly powerful for organisations already using FortiGate firewalls and FortiAnalyzer – enabling a genuinely unified security architecture with shared telemetry across the entire stack.
Key features:
- Pre-Execution Threat Prevention: Blocks malicious behaviour before code can execute, reducing breach impact to near zero.
- Real-Time Event Correlation: Correlates endpoint events with network and firewall telemetry through the Fortinet Security Fabric.
- FortiGate + FortiAnalyzer Integration: Native integration provides unified visibility and centralised investigation across the Fortinet ecosystem.
- Automated Playbooks: Pre-built incident response playbooks enable rapid, consistent containment across large environments.
- Low Operational Overhead: Lightweight agent and policy templates designed for lean IT teams managing distributed endpoints.
9. Trellix
Best for: Large-scale SOC environments requiring advanced detection with sandboxing
Trellix – born from the merger of McAfee Enterprise and FireEye – has fully integrated its combined capabilities into a mature detection and response platform. Its dynamic telemetry, integrated sandboxing, and adaptive response mechanisms make it well-suited for large enterprise and government SOC environments with high-volume, complex threat landscapes.
Key features:
- Dynamic Threat Intelligence: Combines McAfee’s prevention heritage with FireEye’s renowned threat intelligence and incident response expertise.
- Integrated Sandboxing: Detonates suspicious files and URLs in an isolated environment for deep behavioural analysis.
- Adaptive Response: Response mechanisms that adjust automatically based on threat severity and asset criticality.
- Trellix XDR: Extends telemetry collection across email, network, cloud, and endpoint in a converged view.
- Government & Enterprise Grade: Meets compliance requirements for highly regulated industries, with FedRAMP-authorised cloud deployment options.
How to Choose the Best EDR Tool?
Every organization is different. What works for a multinational may overwhelm a mid-size firm. Here’s how to make your decision:
| CRITERION | WHAT TO EVALUATE |
| Detection Capabilities | Behaviour-based, signatureless & AI/ML-driven detection. Check MITRE ATT&CK technique coverage in vendor documentation. |
| Response Speed | Automated response workflows, rollback features, and endpoint isolation. Look for sub-second containment claims with independent test backing. |
| Integration Flexibility | Compatibility with your existing SIEM, firewall, IAM, and cloud platforms. Native XDR extension is a strong plus. |
| Ease of Use | Dashboards, policy management, and alert investigation should be intuitive — especially if your team is not SOC-heavy. Review G2 and Gartner Peer Insights ratings for ease-of-use scores. |
| MDR / Support Services | Some vendors offer Managed Detection and Response (MDR) as a service — a game-changer for overburdened internal teams. |
| Pricing Transparency | EDR typically costs $40–$100 per endpoint per year. Compare this against the average ransomware recovery cost (over $150,000 for SMBs) to justify budget. |
| Compliance Alignment | Verify the tool supports your regulatory requirements — ISO 27001, RBI, SEBI & CERT-In in India and PCI DSS, HIPAA, GDPR, or sector-specific frameworks. |
What Are Open-Source EDR Tools?
Open-source EDR tools offer customisable, budget-friendly options – particularly valuable for research environments, training labs, and organisations with in-house engineering capability. However, these tools generally lack the managed services, automated response depth, and vendor support of commercial platforms.
| Tool | Key Features | Best For | Limitations |
| OSSEC | Host-based IDS, log analysis, rootkit detection | SMBs, compliance-focused | No real-time response |
| Wazuh | SIEM + EDR, agent-based monitoring, cloud support | Mid-size environments | Complex configuration |
| Security Onion | EDR + NIDS/NIPS, Elastic Stack integration | Research, MSPs | Heavy system requirements |
| Velociraptor | Endpoint visibility, threat hunting, IR tools | Blue teams, researchers | Steep learning curve |
| GRR Rapid Response | Forensics and live response toolset | DFIR professionals | Less intuitive for beginners |
| LimaCharlie | Cloud-native sensor, real-time telemetry, API-first architecture | Developers, MSSPs building custom detection pipelines | Requires engineering effort to operationalise |
The Future of EDR Tools: AI, Agentic Threats & What Comes Next
The emergence of AI and agentic threats is fundamentally reshaping how businesses will evaluate and deploy EDR tools.
As attackers leverage generative AI to create polymorphic malware at scale and autonomous agents to chain legitimate actions into destructive outcomes, the traditional EDR selection criteria will change. Detection accuracy, response speed, and ease of deployment will expand to include entirely new dimensions.
For example – Can the tool detect AI agent behaviour? Does it provide visibility into MCP session activity? How does it handle prompt injection risks originating from endpoint data?
Simultaneously, AI is making EDR platforms significantly more powerful, with LLM-driven investigation, autonomous triage, and predictive threat modelling reducing the burden on lean security teams. The net result is that businesses will increasingly select EDR not just on what threats it can stop today, but on how intelligently and autonomously it can adapt to threats that did not exist yesterday. This will make AI readiness, agentic threat visibility, and MDR integration the defining selection criteria of the next generation.
Why a Trusted MDR Partner Like CyberNX May Be the Smarter Choice
The tools listed above represent the best standalone EDR platforms available today. But for most mid-market firms and growing enterprises, the more important question is not which EDR tool to buy but who should operate it.
Most organisations lack the in-house expertise to fully operationalise an advanced EDR platform, and that is precisely where a MDR partner like CyberNX changes the equation entirely.
CyberNX embeds Managed Detection and Response (MDR) directly into its delivery model. What this means is that clients get not just the technology, but expert-led monitoring, continuous threat hunting, and proactive incident management as a single offering.
Our EDR, built on the Elastic Defend MDR platform, acts as a co-pilot for security operations, combining:
- AI-Powered Investigations: Automated and analyst-guided detection that surfaces real threats fast, cutting through noise before it becomes a crisis.
- User Behaviour Analytics: Continuous baselining of user activity to catch insider threats, compromised credentials, and abnormal access patterns.
- Tailored Regional Threat Intelligence: Contextual intelligence drawn from global trusted networks, local APT behaviour, and regional sector vulnerabilities – delivering relevant, low-noise detection that generic platforms often miss.
- Real-Time Threat Containment: Automated, analyst-led, and community-driven playbooks isolate compromised endpoints instantly, before attackers can cause business disruption.
- Zero Complexity Deployment: Lightweight agents, cloud-first architecture, and policy templates make onboarding seamless – even for lean IT teams without a dedicated SOC.
- Compliance-Centric by Design: Built-in support for ISO 27001, PCI DSS, and CERT-In, with sector-specific coverage for BFSI, healthcare, and government organisations.
What makes this model particularly compelling is the value alignment. As clients grow, we scale proportionally, understanding that security needs evolve with the business, not against it. For IT leaders weighing enterprise-grade protection against budget realities, the choice is rarely just about the tool. It is about who stands behind it. CyberNX offers both: the platform and the expertise to make it work, without the bloated pricing that typically comes with either.
Conclusion
Are you aiming to safeguard an enterprise or an agile tech startup? In the current threat environment where cyberattacks are sophisticated, discrete in approach and targeting every kind of business, choosing the right EDR tool can make or break your incident response readiness.
CyberNX’s EDR services offer localized intelligence, real-time response and human-backed expertise, making it a security leader for organizations in India and beyond seeking practical and scalable protection across endpoints. Contact us today!
EDR Tools FAQs
Can EDR security tools detect insider threats?
Yes. Modern EDR platforms analyse user behaviour and access patterns, allowing them to flag unusual internal activity, often the hallmark of insider threats.
Are cloud-based EDR tools secure for sensitive environments?
Cloud-native EDR solutions use encrypted communication, data isolation, and compliance-ready frameworks to secure even highly regulated environments like healthcare and finance.
What’s the difference between EDR and antivirus?
While antivirus tools scan files for known signatures, EDR tools monitor behaviours, analyse system events, and offer real-time response capabilities – even against unknown threats.
Is EDR enough, or do I need XDR too?
EDR focuses on endpoints. XDR extends visibility across email, identity, cloud, and network layers. If your environment is complex and multi-vector attacks are a concern, XDR offers a broader defence. Learn everything about the modern endpoint security tool with our blog XDR guide.