Find most critical weaknesses with
Vulnerability Assessment (VA) Services
Our expert-led analysis and advanced automation deliver comprehensive Vulnerability Assessment services that identify, prioritise and mitigate security gaps across your IT environment.
Request a Free Demo




















INTRODUCTION
Fortify your Digital Environment with CyberNX Vulnerability Assessment Services
Based on the latest threat intelligence and unique business context, we identify vulnerabilities in systems such as software, networks and apps and prioritise remediation effectively.
We Solve Your Key Pain Points:
Undiscovered security flaws in applications, networks and devices can become entry points for attackers. We uncover what automated tools may miss.
Not all vulnerabilities pose the same risk. We rate threats based on impact, likelihood and business context, so you can act where it matters.
Our thorough assessments help you stay aligned with key standards like ISO 27001, PCI-DSS and GDPR by flagging non-compliant security controls.
Security teams are stretched thin. We act as an extension of your team, offering depth, precision and dedicated attention to catch vulnerabilities.
Fragmented environments can hide critical weaknesses. Our assessment provides a holistic view of your asset landscape and threat exposure.
PROCESS
How It Works?
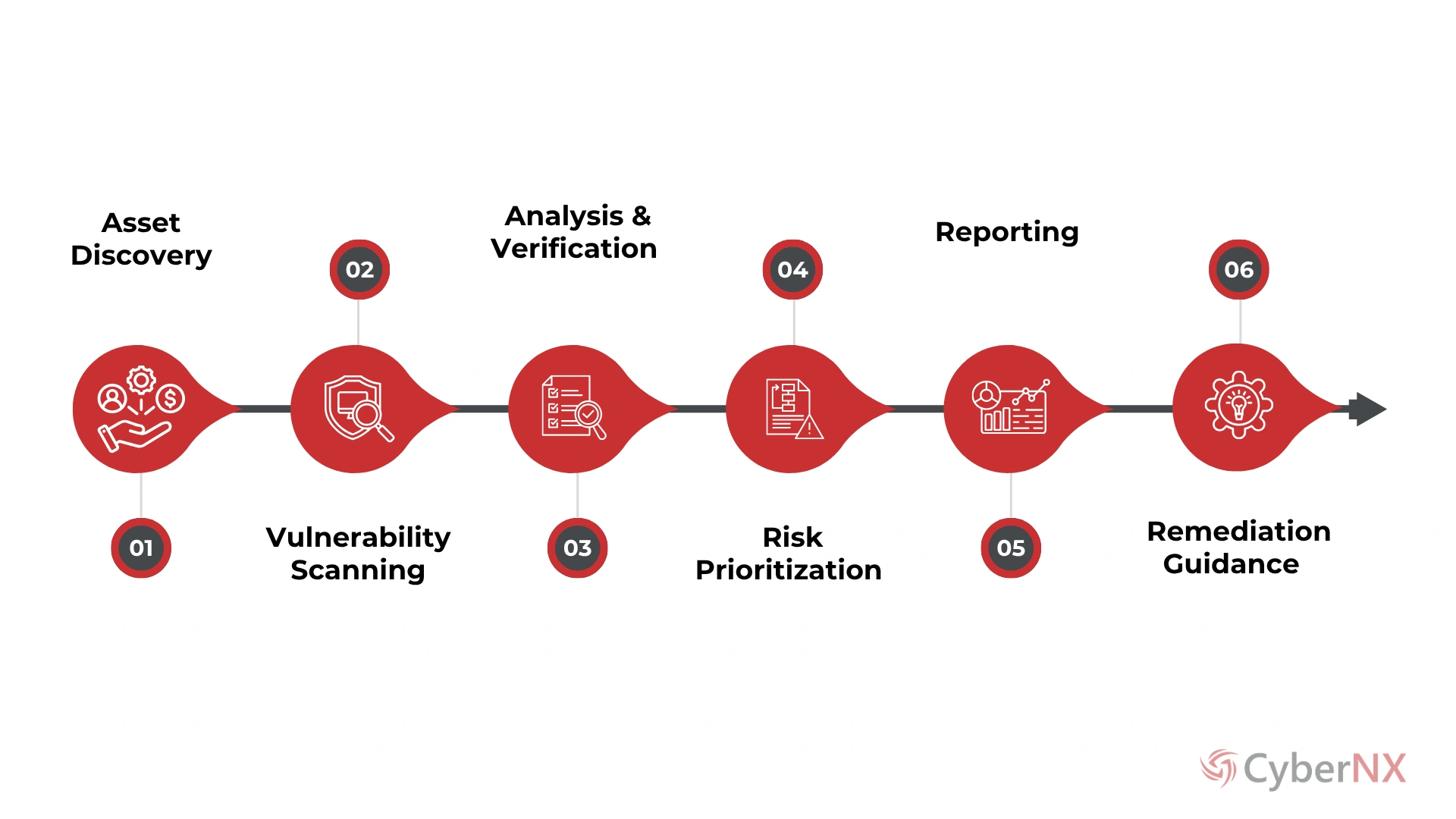
Looking for Vulnerability Assessment Services? Count on our experts.
APPROACH
Why Choose CyberNX for Vulnerability Assessment Services?
Vulnerability Assessment is the bedrock of defence, and we make it strong by going beyond surface-level scanning, powering it with technology and delivering actionable insights that help organisations enhance their cyber resilience.
Advanced Tools
Our experts use advanced and cutting-edge Vulnerability Assessment (VA)tools and technologies for testing.
CERT-IN Empanelled
Recognised by CERT-IN, our team follows best practices and standards to perform vulnerability assessments.
Risk Mitigation
Our VA team identify and help remediate vulnerabilities to mitigate risks and strengthen cyber defences.
Skilled Team
Our skilled team has performed vulnerability assessments for clients across India and other countries.
Regulatory Compliance
We ensure that security testing meets compliance needs of regulatory bodies like CERT-IN, SEBI and RBI.
Customer first Approach is our guiding principle.
BENEFITS
Measure the Strength of Your Security Posture with our VA Services
Expert Guided Automation
We combine expert insight with automation to uncover relevant vulnerabilities while reducing false positives.
Context Aware Testing
Our assessments are aligned with your architecture, workflows and industry to deliver meaningful results.
Faster Risk Mitigation
We prioritise and address critical threats quickly to minimise downtime, data loss and reputational harm.
Compliance Ready Reports
Mapped to major standards, our reports help you show due diligence and stay prepared for any audit.
Security Focused Strategy
We deliver insights that support smart security planning and align defences with your business goals.
For Customized Plans tailored to Your Needs,
Get in Touch Today!
FAQs
Frequently Asked Questions
VA identifies and ranks known security weaknesses across your systems, while a penetration test simulates real-world attacks to exploit those vulnerabilities. VA is broader and more continuous, offering regular visibility into your security posture. Penetration testing is point-in-time and focuses on demonstrating actual exploitation.
Ideally, assessments should be conducted quarterly or after any major system change. However, organizations with dynamic IT environments or regulatory requirements may need more frequent scans to maintain a strong security posture.
Yes. Regular VA supports compliance with standards like ISO 27001, PCI-DSS and HIPAA by identifying non-compliant configurations and gaps. Reports from VA can serve as evidence during audits and demonstrate proactive risk management.
VA can be performed on a wide range of assets including servers, web and mobile applications, cloud infrastructure, APIs, endpoints and network devices. A comprehensive assessment ensures full visibility into potential exposure areas across your environment.
RESOURCES