SEBI CSCRF Deadline Extended. Secure Your Organization NOW!
The Securities and Exchange Board of India (SEBI) has recently provided much-needed relief to Regulated Entities (REs) by extending the
Contents
Cyberattacks are a constant threat. But what if you could fight fire with fire? Penetration testing methodologies are the tools that let you do just that! Penetration testing methodologies are structured frameworks that guide security professionals through the process of identifying and exploiting vulnerabilities in systems and networks. They provide a systematic approach to simulating real-world cyberattacks, allowing organizations to proactively strengthen their defenses.
In cybersecurity, consistency and precision are vital. Penetration testing methodologies provide the necessary framework, ensuring a standardized and repeatable process. This consistency is crucial for tracking security posture and measuring mitigation effectiveness. Without a structured methodology, testing risks becoming chaotic, potentially missing critical vulnerabilities and leading to incomplete risk assessments. A well-defined methodology, however, provides a clear roadmap, ensuring all steps are taken and no crucial aspect is overlooked. This structured approach not only enhances thoroughness but also ensures reliable and actionable results, allowing organizations to confidently prioritize remediation efforts.
Here are five prominent pen testing methodologies and standards:
OWASP is a non-profit foundation that works to improve the security of software. It provides a wealth of resources, including the OWASP Testing Guide and the OWASP Top 10, which identifies the most critical web application security risks.
Who Needs OWASP?
Web application developers, security testers, and organizations that rely on web applications. OWASP’s resources are essential for securing web-based systems.
NIST provides standards, guidelines, and best practices for cybersecurity. NIST’s Special Publication 800-115, “Technical Guide to Information Security Testing and Assessment,” is a key resource for penetration testing.
Who Needs NIST?
Government agencies, organizations in regulated industries, and any entity that requires a robust and standardized approach to security testing.
OSSTMM is a comprehensive methodology that covers various aspects of security testing, including information, process, internet, wireless, and physical security. It emphasizes a scientific approach to security testing.
Who Needs OSSTMM?
Security professionals who require a detailed and rigorous testing methodology, particularly those involved in comprehensive security assessments.
PTES is a standard that outlines seven phases of penetration testing, from pre-engagement to reporting. It provides a detailed framework for conducting thorough and consistent penetration tests.
Who Needs PTES?
Penetration testers, security consultants, and organizations that want a structured and comprehensive approach to penetration testing.
ISSAF provides a detailed framework for conducting security assessments, including penetration testing. It covers various aspects of security, from information gathering to vulnerability analysis and exploitation.
Who Needs ISSAF?
Experienced security professionals and organizations that require a deep and thorough security assessment methodology.
While methodologies vary, they typically include these core stages in Penetration Testing Process:
Penetration testing methodologies are fundamental for robust cybersecurity. These methodologies enable in-depth security evaluations, systematically uncovering vulnerabilities that might be missed in ad-hoc testing. By following a structured approach, organizations gain a comprehensive understanding of their security posture, allowing them to prioritize remediation efforts effectively and ultimately strengthen their defenses against real-world cyber threats.
CyberNX takes a unique approach to penetration testing by mimicking real-world hacker techniques. This allows for a deeper level of testing, uncovering vulnerabilities that traditional methods might miss. By simulating advanced persistent threats (APTs) and other sophisticated attack vectors, CyberNX provides a more realistic assessment of an organization’s security posture. This approach ensures that even the most well-hidden weaknesses are identified and addressed.
Penetration testing methodologies are essential for any organization that wants to maintain a strong security posture. By providing a structured and comprehensive approach to security testing, these methodologies help organizations identify and mitigate vulnerabilities before they can be exploited by malicious actors.
Selecting the right methodology depends on your organization’s specific needs and requirements. Consider factors such as the scope of the test, the type of systems being tested, and the level of expertise required.
Enhance your security posture today! Contact CyberNX for a comprehensive penetration testing assessment tailored to your organization’s needs. Learn how our hacker-style techniques can uncover hidden vulnerabilities and strengthen your defenses.
Share on
RESOURCES
The Securities and Exchange Board of India (SEBI) has recently provided much-needed relief to Regulated Entities (REs) by extending the
In the fast-paced world of cybersecurity, staying ahead of evolving threats requires more than just reactive measures. CISOs, CXOs, and
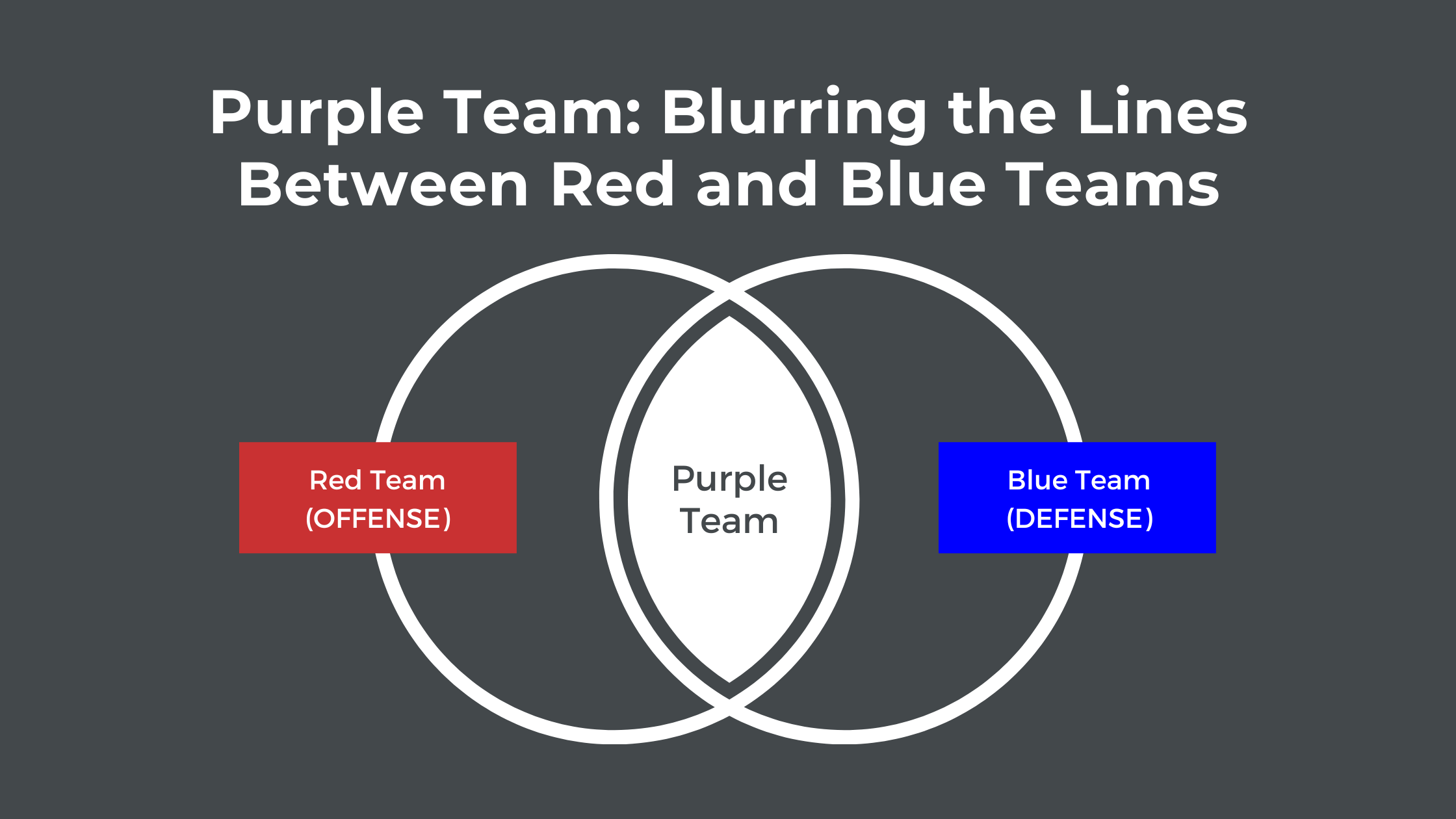
In the ever-evolving landscape of cybersecurity, CISOs, CXOs, and IT Managers are constantly seeking innovative strategies to fortify their defenses.
RESOURCES
Cyber Security Knowledge Hub
Copyright © 2025 CyberNX | All Rights Reserved | Terms and Conditions | Privacy Policy